Huawei’s 5G Gambit: Sharing Tech Won’t Fix Security
Posted on

Huawei HQ in Shenzhen, China
WASHINGTON: Even if Huawei is 100 percent sincere about sharing its trade secrets — a tremendous ‘if’ — a 5G network built on Chinese technology would still be more vulnerable to Chinese hacking than one designed entirely in the West.
It’s like buying a house. Of course you’ll change all the locks when you move in. You can even renovate and build new walls. But you may never find all the surprises the previous owners left behind — and someone else will always have the blueprints for where you live.
Any Western company that licensed Huawei’s 5G technology would have to comb through the code to root out hidden backdoors —then do it all over again every time the Chinese company released an update. Even if Huawei cooperates unreservedly, bringing its vulnerable, buggy firmware up to Western standards could be prohibitively expensive. And even if you could clean up the code, you’d still be using tech that Chinese hackers knew inside and out.
So almost everyone we spoke to doubted Huawei would ever be a trustworthy partner. Even the most optimistic expert we interviewed, Finite State CEO Matt Wyckhouse — a cybersecurity pioneer who’s called Huawei’s products “some of the worst devices we’ve ever tested” — warned any would-be licensee should approach a deal with fear and trembling.
“There were security and quality issues that were rampant throughout that code,” Wyckhouse told me this morning. “Whoever’s going to license that technology needs to know they have a lot of work ahead of them to really remediate those issues.”
“It’s definitely possible. It’s a question of how much time and money you need to invest,” Wyckhouse said. “It’s not insurmountable as long as Huawei is planning to license all of their code as part of a deal, so that an expert security engineering team” — an independent team — “can come in and make those fixes.”
“If they won’t let you do that,” he said, “that would probably be a deal breaker for me.”

Ren Zhengfei
How It Could Work
Would Huawei agree to share its source code? Perhaps. New York Times columnist Thomas Friedman broke the news of Huawei’s offer on Tuesday after an interview with company CEO and founder Ren Zhengfei. But a subsequent story in the Economist offered much more detail — although there’s still not much to work with:
“For a one-time fee, a transaction would give the buyer perpetual access to Huawei’s existing 5G patents, licenses, code, technical blueprints and production know-how. The acquirer could modify the source code,” the Economist wrote. “Huawei would likewise be free to develop its technology in whatever direction it pleases.”
So the deal probably would include the source code — or rather, one specific instance of that code. But software and firmware require constant updates to keep up with changing technology. That leaves a licensee with two options, both of them expensive:
- Do all the updates in-house, which means building up your own corps of software engineers who understand the Huawei code as well as Huawei itself does and can update it as rapidly as Huawei can, so you don’t fall hopelessly behind.
- Go back to Huawei and pay another “one-time fee” to get access to the updated source code, which you then have to check for vulnerabilities. Repeat ad infinitum each time the Chinese company issues an update.
Yes, it is possible to find vulnerabilities without seeing the source code. Hackers do that all the time. Wyckhouse’s company can exhaustively analyze the machine-readable 1s and 0s — the “binaries” — that actually run on each device. But it’s much easier to find problems if you’re looking at the source code, which unlike machine code can be read and understood by humans, if those humans have the proper training.
Most of the vulnerabilities Wyckhouse & co. found in Huawei firmware — a whopping 102 in the average device — are fairly obvious and easy to remove, he said. That includes hidden backdoor accounts and cryptographic keys that allow unauthorized users to log in. Less obvious bugs like buffer overflows — which let a hacker disguise unauthorized commands as legitimate inputs — are a little harder to find and fix, but still entirely doable.
The long-term problem is you have to check everything all over again every time Huawei changes anything. Even if you have detailed audit logs showing exactly what code was edited — which assumes Huawei will provide complete and accurate logs — you can’t just look at the parts that changed, because a seemingly innocent piece of new code could interact with old code in unexpected and dangerous ways.
“Every time they issue a firmware update,” Wyckhouse said, “you have to redo your security analysis because it’s hard to know what’s change.”
Even if Huawei’s intentions are entirely pure, most software vulnerabilities arise from sloppy, buggy coding, not deliberate backdoors — and Huawei’s programming is often sloppy. So, Wyckhouse said, any licensee should get a firm commitment from Huawei to fix such quality control issues at its own expense, rather than require the licensee to do all the heavy lifting.
“This deal would be incredibly complex,” Wyckhouse said. “I think it could work, if the right buyer is there and they recognize the entire set of costs associated with this, and they can build a business around it with those costs in mind …but I would make sure any buyer that’s considering this really understands the hidden costs.”
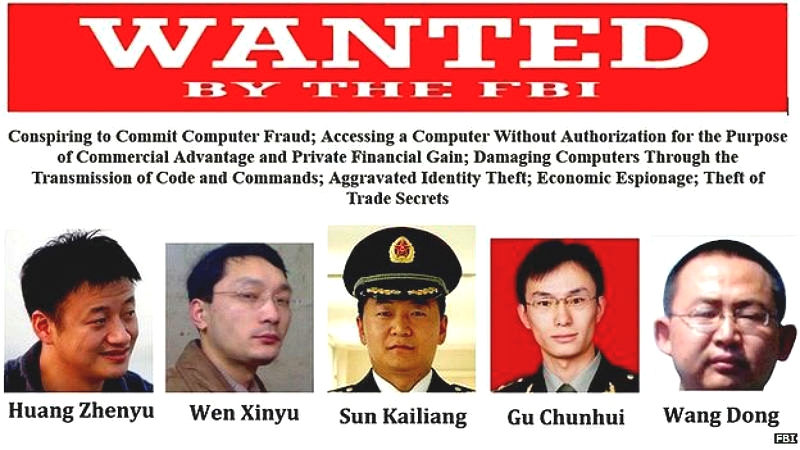
Chinese hackers publicly named as suspects by the FBI
Why It Wouldn’t Work
While it might be technically feasible to fix the code if you had Huawei’s full cooperation, most of our sources doubt the Chinese company would ever be a trustworthy partner.
“There’s no way in hell they’re giving up their IP [intellectual property] without having leverage,” said one intelligence community veteran. “They say Huawei’s going to give me all their intellectual property, allow me to adjust it at will, and completely copy it, out of the goodness of their hearts? No way.”
“This is the People’s Liberation Army talking. Huawei is the PLA,” the IC veteran warned. “Saying [they’re] going to give up source code for review sounds good — but you’re still installing PLA gear as your communications backbone.”
Huawei founder Ren worked for the PLA from 1974 to 1983, but he never held a formal military rank. The pro-Beijing South China Morning Post describes his role as a non-military civil engineering job, roughly equivalent to the US Army Corps of Engineers.
But the bigger concern is current Chinese law requiring IT companies to give full access to the security agencies.
“I think it’s an unserious public relations ploy,” agreed Andy Keiser, a former Hill intelligence staffer who’s now a senior fellow at GMU’s National Security Institute.
“Were they actually serious, [it] would allow Huawei gear to be deployed in networks around the world without the Huawei stigma,” Keiser said. But it wouldn’t make the technology secure, he argued: “Vulnerabilities and back doors written by Huawei coders would be near impossible to identify. It’s like trying to find a needle in a stack of needles.”
“How much work would it take to go in and get all the bugs of Huawei’s stuff?” the IC vet concurred. “By the time you get that done, just build your own goddamn system.”
Another GMU senior fellow, Bryan Smith, shared this skepticism about Huawei’s intentions. So what are the Chinese really after?
“I believe Ren and the Chinese Communist Party are trying to avoid two things with this admittedly clever approach,” Smith told me. First, he said, they want to stop President Donald Trump from cutting off Huawei’s access to American suppliers. Second, they want to limit “the splintering of the Internet” and future 5G networks into two blocs, in which only China’s client states bought its high-tech products, while the larger and wealthier part of the world relied on Western tech.
Selling to more countries, and more prosperous ones, would not only help Huawei’s bottom line, Smith said: It would also create “a huge surface area for Chinese signals intelligence and cyber operations.” Even if Western licensees managed to patch the vulnerabilities in Huawei’s code, it would still be an easier target for Chinese intelligence than code developed without any Chinese input at all.
It’s a math problem. In rough terms, Huawei’s technology as-is might be 100 percent vulnerable to Chinese penetration, but that doesn’t do Chinese intelligence much good if only 10 percent of the planet is willing to buy it. Better to share the technology and let Western licenses come up with a version that’s only 10 percent vulnerable to penetration but is used by 100 percent of the world.
That’s a lousy deal for the West, our experts argued, especially since 5G networks won’t just underpin the cellular network but a host of other Internet of Things applications from self-driving cars to surveillance.
“5G’s not like any other cellphone technology,” the intelligence community veteran warned. “It’s the keys to the kingdom. It’s insane to give that level of control to another nation-state.”
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.
