Troubled JRSS Cyber System Exposes DoD Data, Says DoD IG
Posted on
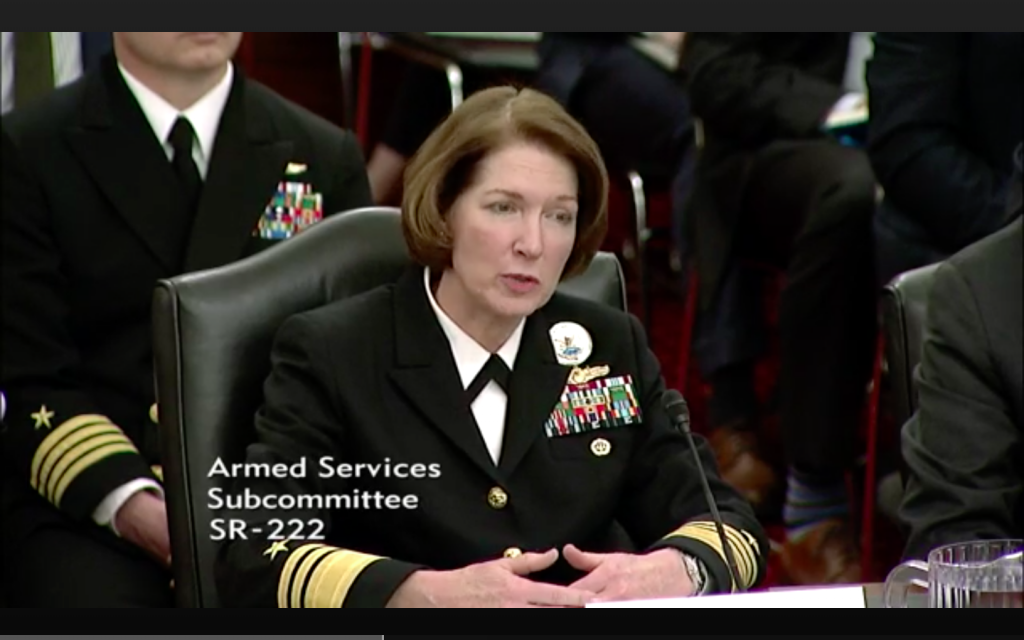
Vice Adm. Nancy Norton
The Joint Regional Security Stacks (JRSS) program is one of the Defense Departments most vital cybersecurity initiatives, designed to consolidate disparate networks on posts, camps and stations into a handful of regional networks under a single security architecture that can be better monitored and defended against attack. The program, however, has been plagued by persistent problems since its inception, and a DoD Inspector General report out this week says the program’s travails continue.
For example, cybersecurity safeguards for the JRSS are not being met so DoD data is at risk. Operators don’t have the tools they need to properly monitor and troubleshoot the system, nor the training to run it properly. And formal capability requirements and an approved test and evaluation master plan are lacking, so JRSS functionality isn’t optimum.
The danger presented by JRSS failings cited in the audit can be extreme.
“The JRSS is the most critical near‑term element of the DoD’s JIE,” states the audit report released Tuesday. “Therefore, if the JRSS is not operationally effective, secure, and sustainable, the DoD may not achieve the (Joint Information Environment) vision, which includes achieving greater security on the (DoD Information Network). In addition, without adequate security safeguards for the JRSS, weaknesses identified in this report could prevent network defenders from obtaining the information necessary to make timely decisions, and could lead to unauthorized access to the DoDIN and the destruction, manipulation, or compromise of DoD data.”
The DoD IG’s concerns parallel those expressed by the Office of the Director, Operational Test and Evaluation (DOT&E) in it’s FY18 annual report issued in early 2019. That report recommended that JRSS deployment be halted after JRSS operators failed to detect a cyber attack by the Air Force’s 177th Information Aggressor Squadron. “The DOD Chief Information Officer and the services should discontinue deploying JRSS until the system demonstrates that it is capable of helping network defenders to detect and respond to operationally realistic cyberattacks,” DOT&E wrote.
Without calling for a program pause, the most recent DoD IG report digs deeper into some of the underlying causes for JRSS’ performance issues. It attributes most of the JRSS failings to the fact that the program was categorized as a “technology refresh” rather than a “major automated information system acquisition”, which significantly lessened requirements before rolling out the system. Under DoD Instruction 5000.02, acquisitions of automated information systems that are estimated to exceed $520 million from the first phase of acquisition through sustainment are to be considered Major Automated Information Systems (MAIS) programs.
“Although the JRSS was estimated to cost over $520 million, DoD officials considered the JRSS to be a technology refresh and, therefore, not subject to DoD Instruction 5000.02 requirements,” states the audit. “Had DoD Instruction 5000.02 requirements applied, the JRSS would have qualified as a major automated information system acquisition because it is projected to cost $1.7 billion more than the $520 million threshold and DoD officials would have been required to develop formal capability requirements, an approved test and evaluation master plan, and a training plan for operators during the development of the JRSS.”
The report points out that capability requirements, test and evaluation plans, and training are the elements “which help ensure that the product meets users’ needs”.
On whether it was mistake to call JRSS a technology refresh, “JRSS should have fallen somewhere between a technology refresh and a MAIS acquisition,” David Mihelcic, former DISA chief technology officer and now a consultant with DMMI, told Breaking Defense, adding that he agreed “overall” with the findings of the report. “While JRSS is an integration of proven commercial off the shelf technology, it also attempted to centralize massive amounts of traffic at a scale never attempted before by a DoD organization.
“A MAIS approach may have been overkill, causing the program to slow to a point where it could not meet schedule needs of the Army. However JRSS could have benefited by an enhanced testing and incremental acquisition approach–buy a little, test a little, field a little. This approach could have highlighted scale and reliability issues before the lion’s share of funds were invested.”
The JRSS is a suite of equipment that includes network routers, firewalls, and switches designed to provide network security capabilities such as intrusion detection and prevention, reduce the number of access points to the DoDIN, enable inspections of network traffic that travels through the JRSS, serve as the network traffic flow integration point between DoD components, and facilitate the monitoring and control of all security mechanisms throughout the DoD network.
The program is managed by the Defense Information Systems Agency (DISA), which has agreed to “address all specifics of (DoD IG’s) recommendations”, according to the audit report. Recommendations include: proposing a plan to address changes identified during testing after a “measures of performance” assessment; and working with DoD Officials to incorporate JRSS operational training requirements into the service components’ institutional training programs, according to the audit. A third recommendation DISA agreed to enact was redacted in the report.
In her keynote address at AFCEA’s TechNet Cyber conference in mid-May, DISA Director Adm. Nancy Norton offered some specific actions DISA will take to “address reoccurring operational and technical issues our technical partners experienced.”
In the area of training, DISA created “10 on-demand operator training videos, trained 169 defensive cyber operators, and provided the military services 15 programs so they can develop their own training,” said Norton.
Regarding migration, “our team simplified the customer migration process with standardized roles, simplified account provisioning, and prerequisite migration checklists. We modified the SIPRNet system in preparation for migration to use the same tools as NIPRNet for trouble ticket management , fault detection, and performance monitoring and management.”
To improve reliability and stability, “we reconfigured the joint management systems tools and doubled the virtual desktop infrastructure capacity. The JRSS team standardized the security information and event management architecture and upgraded critical devices to improve performance.”
DISA also assessed JRSS operational policy, process, and governance by “developing best practices for the firewall, intrusion prevention system, and intrusion detection system to optimize the use of tools across the defensive cyber operations community,” she said.
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.
