A ‘Solarium’ For Hacking: Sen. King Launches Cyber Strategy Panel
Posted on
WASHINGTON: The US lacks a strategy for cyberspace, Sen. Angus King declared today, something many experts would agree with. So Congress is convening a high-level commission consciously modeled on President Eisenhower’s 1953 famous Solarium effort that chose the path of containment the US followed, successfully, for the next 36 years.
“I’ve been engaged in this issue on both Armed Services and Intelligence [committees] for five years and one of the things I’ve concluded is, we’re a cheap date when it comes to cyber,” King told reporters this afternoon. “People can go after us… and not really expect much in the way of a response, whether it’s the Chinese OPM attack or the Russian attack on our elections or… Anthem, Blue Cross, Sony Pictures.
“We want to look at a comprehensive picture,” King said. “One of the motivations of this is that, right now, the cyber responsibility is scattered throughout the federal government. There’s no central leadership and there’s no policy that our adversaries — or our allies for that matter — can discern about what we’re going to do in a particular situation…. until we clarify that, we’re going to keep getting hit.”
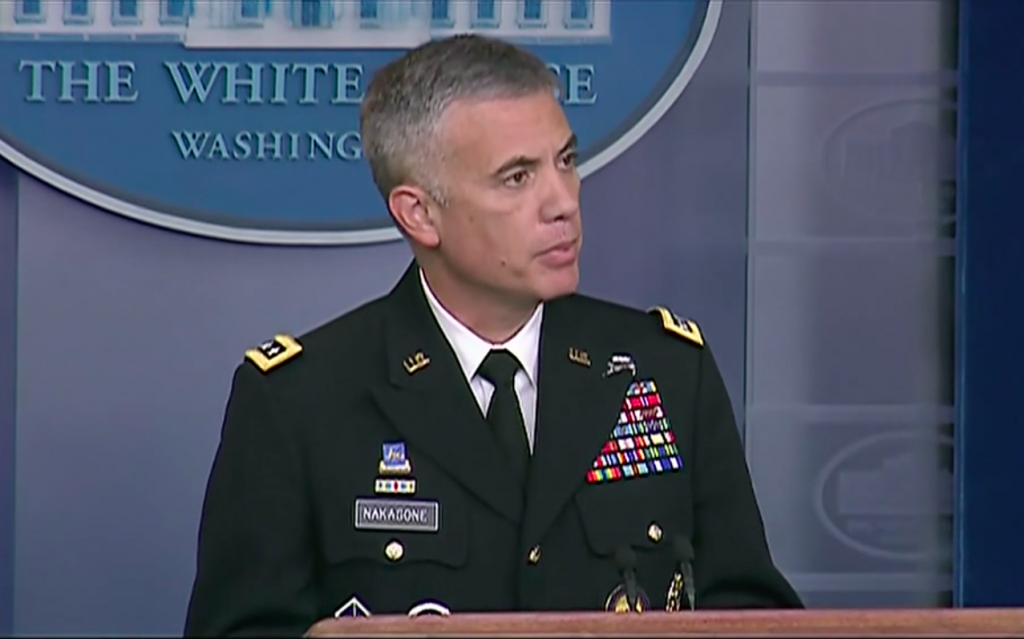
Like the original Project Solarium, King’s commission will split into three teams to examine three alternatives: deterrence; persistent engagement (as championed by Cyber Command chief Gen. Paul Nakasone); and international agreement on some kind of “Geneva Convention of cyber.” King emphasized those alternatives aren’t mutually exclusive, and the final recommendations for new policy and legislation may be a blend.
No Trump
Now, President Trump has not seized the helm here the way Eisenhower did. Unlike its inspiration, the Cyber Solarium is a congressional initiative, mandated by last year’s National Defense Authorization Act, so the recommendations it produces aren’t guaranteed a hearing in the White House.
But the 14-member commission does include four very genuinely senior decision makers:
- the acting deputy secretary of defense, David Norquist;
- the acting deputy secretary of homeland security, David Pekoske;
- the deputy director of National Intelligence, Susan Gordon; and
- the director of the FBI, Chris Wray.
It’s also co-chaired by Sen. King, an independent who caucuses with the Democrats, and Republican Rep. Mike Gallagher. Its other members include two more legislators, Sen. Ben Sasse and Rep. Jim Langevin; Tom Fanning, CEO of Southern Company, a major utility; and an assortment of experts and ex-officials.
King says these influential commissioners are actually showing up and engaging in “very, very serious… very substantive” discussions. So there’s some solid ground for hope that this congressionally-mandated study won’t just sink below the water without a ripple like so many others before. At the very least, it should forcibly expose senior administration officials to the kind of big-picture thinking for which their regular schedule of crisis management and budget battles leaves little time.
King plans to split the 14 commissioners into three teams — the rosters aren’t set yet — to pursue three strategic options, followed by a general discussion in September or October, followed by the final report before December ends. He didn’t want to prejudge the discussions, but he did offer an outline of the problem.
Three Strategies
The most obvious response, drawing on decades of Cold War balance of terror, is deterrence, which is one of the three strategic options the commission will consider.
“When somebody is sitting in a foreign capital deciding to attack our electoral system, I want somebody at the table saying, ‘ohhhhh, this is gonna cost us,’ because right now I don’t think they’re making that calculus,” King said.
Deterrence includes the threat of retaliation, what theorists call deterrence by punishment: “You hit us, we’re going to hit you back,” as King put it — but, the senator said, it’s got to be more sophisticated than that. It’s much harder to figure out the origin of a computer virus than it is that of a nuclear missile, he noted, and powerful malware is cheap enough that it can be used by terrorists and criminals, who are much harder than a nation-state to target for retaliation — whether in-kind, with a cyber counter-attack, or asymmetrically, with anything from armed force to economic sanctions.
So deterrence must include “deterrence by denial,” King said: building up defenses strong enough that would-be attackers doubt they can overcome them. This has proven impossible so far against a large-scale nuclear strike: It’s not exactly easy for computer networks, but it’s possible, especially, King argues, if the private sector and federal government work together.
It’s also possible, if far from easy, to come to an agreement with potential adversaries. The Chemical Weapons Convention, nuclear arms control talks, and even the Campaign to Stop Killer Robots come to mind. Yes, King acknowledged, arms control agreements are all too often breached — Syrian use of poison gas, Russian development of INF-banned cruise missiles — but “norms and standards” still have value, he argued. “I don’t think that’s entirely what we can rely upon,” he said, “[but] I have felt for a long time there has to be some.”
The third option, and the hardest to define, is “persistent engagement.” Gen. Paul Nakasone, the Army four-star who heads Cyber Command, has spoken of this idea repeatedly, saying that we’re in “constant contact” with adversaries as they probe and hack our systems, so we need to constantly be taking action in response, both defensively through domestic agencies like the FBI and DHS and offensively through Cyber Command and NSA.
“Engagement is something we’ve been working on for the past several years,” Sen. King said today. “We don’t just sit back and take it.” We need, he went on, to make sure “our adversaries understand” we’re aware of what they’re doing and will take action. How aggressive should that action be? King said “persistent engagement” envisions a less dramatic response than “deterrence.”
“The line between persistent engagement and deterrence is not a bright one and there may be some elements of both,” he said.
So, I suggested, struggling to get the difference, engagement is pushing back, deterrence is hitting back?
“I’ll use that,” King said, chuckling.
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.