End Of Passwords: DISA Tests Walkabout Identity System
Posted on

John Wayne walks Credit: The Searchers
BALTIMORE: Not too many people are known by their gait. There’s John Wayne’s sideways swagger, Charlie Chaplin’s waddle, and Secretariat’s 24-foot stride. The truth is, though, that everyone has a unique gait–just as they have a one-of-a-kind fingerprint and retina pattern. And like fingerprints and eyeballs, a person’s gait or how their mobile device bounces around in their pocket can be another effective method of authentication.
Gait is one of dozens of attributes of authentication that the Defense Information Systems Agency (DISA) is studying in a prototype program to secure the endpoints (re: mobile devices) of a network perimeter. With responsibility for defending the DoD Information Network (DoDIN), the pilot is getting attention at the top of the agency.
“Our vision is to eliminate passwords, said DISA Director Vice Adm. Nancy Norton in her keynote address this week at AFCEA’s TechNet Cyber conference here. “Continuous multi-factor authentication (CMFA) will run seamlessly in the background allowing access through biometric data distinct to each user.”
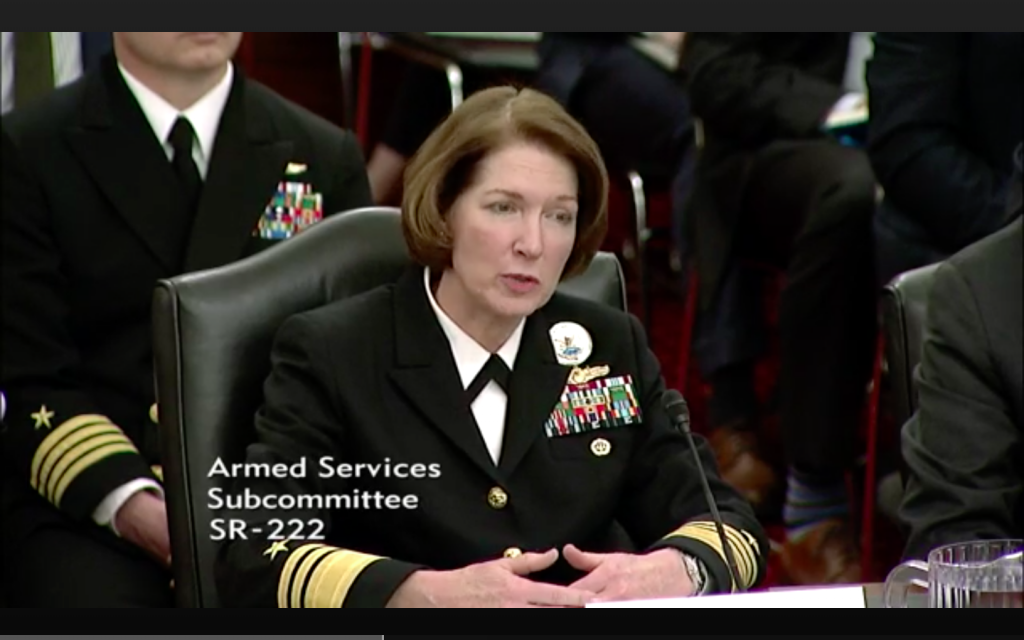
Vice Adm. Nancy Norton
DISA is procuring prototype mobile devices with Qualcomm’s SnapDragon 845 chipset (also used in Samsung’s flagship Galaxy 9 devices) under its first use of DoD’s new Other Transaction Authority (OTA) to quickly fund prototype programs up to $250 million. Two years into the program and after 18 months of research, the handsets are now at the Minimally Viable Product stage where they are beginning to meet some user requirements and are garnering feedback for future iterations, noted Norton. Once proven, the authentication capabilities are expected to be employed for personal mobile devices, government furnished equipment for both unclassified and classified communications, Wi-Fi kits, tablets, and laptops and/or desktop computers.
There are two primary steps to the program for assured identity on mobile networks. The first is hardware attestation, where the device itself generates a key to authenticate its hardware and systems.
The second is CMFA that relies on sensor data tied to both biometric factors (fingerprint, facial features, retina, and voice) and contextual factors (connections to Bluetooth devices, Wi-Fi networks, and peripherals like monitors). Machine learning algorithms analyze the mix of behavioral and contextual biometric factors to provide continuous authentication in mobile, desktop, and server environments, and that allows physical and logical access without passwords.
To up their game on the number of biometric factors to be analyzed, they identified 46 hard factors that could possibly be used for authentication, including gait, the way you swipe, and the orientation in which you hold your device, according to Maj. Nikolaus Ziegler, military deputy director of DISA’s Emerging Technologies Directorate, which was recently created to deliver processes, services and capabilities, as well as assess and integrate emerging technologies across DISA.
Each additional factor can raise a user’s trust score, allowing them to access systems and data as per their network privileges and for longer periods of time. Ziegler explained it this way:
“I wake up in the morning and look at my device, (and facial recognition) gives me a low score. That low score allows me to authenticate into my device, and that starts my identity. When I start walking around it connects to my home Wi-Fi, which is a trusted network, and that elevates contextual factors about me. Now I need to send an email, but in order to log into DoD email off my mobile platform I need a medium trust score, which requires additional biometric and contextual factors about me. Once I log in, I may need to encrypt/decrypt an email, which requires a higher level score.”
Some of these additional biometric and contextual factors will eventually be derived from wearables such as watches, rings and necklaces. “How can you put identity on a wedding band that you always have on?” Ziegler wondered, looking forward to the day he could add another trust factor.
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.
