NSA’s Cybersecurity Directorate Is ‘Back to the Future’
Posted on
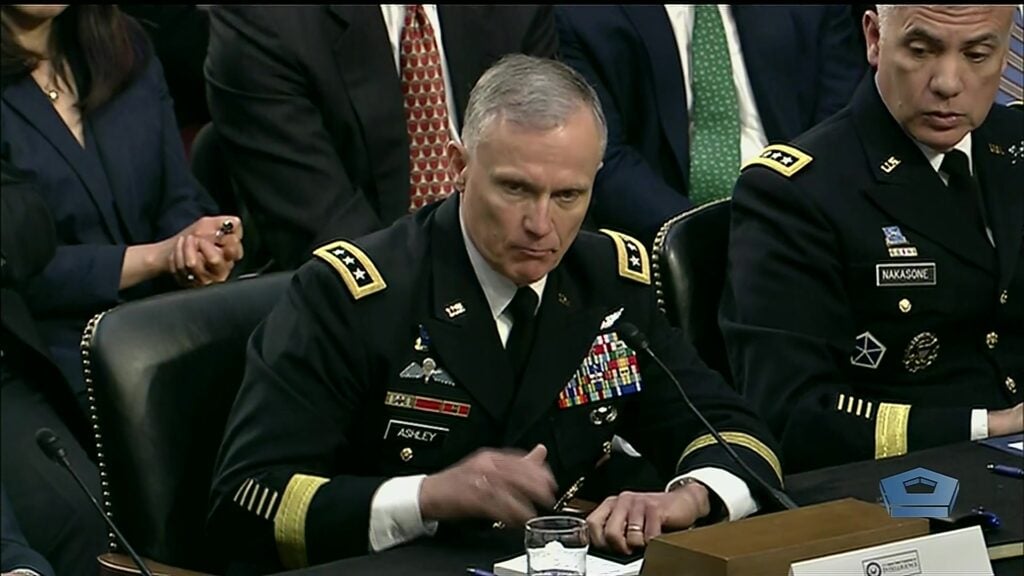
NSA Director and Commander of Cyber Command Army Gen. Paul Nakasone
WASHINGTON: NSA’s creation of a Cybersecurity Directorate is a bit ‘back to the future,’ experts say, in that it unravels the merger between cybersecurity and signals intelligence (SIGINT) operations ordered by former NSA Director Mike Rogers.
NSA Director Gen. Paul Nakasone’s change is “more a restoration of an older model than a transformational event,” one former DoD official says.
Rogers, who led NSA between 2014 and 2018, “dis-established the IAD (Information Assurance Directorate) — the previous institutional home of cyber defense within NSA — during his tenure,” the IC official explains.
Cyber defense was integrated with the directorate responsible for SIGINT “for purposes of operational efficiency,” he said, adding that “plenty of us criticized that decision as IAD was the principal NSA outreach agent to industry, especially to Silicon Valley.”
A former NSA official said that the National Threat Operations Center (NTOC) had performed the cybersecurity role, including outreach, “and was extremely successful both in threat identification and partnerships with the FBI and Homeland Security.” But the elevation of the mission to “its own Directorate raises its stature in NSA to a prominence that is absolutely needed.”
(Maybe it also will help NSA fight back against the Chinese and others who have been stealing its offensive cyber tools.)
Nakasone, who also heads Cyber Command (CYBERCOM), announced the reorganization on June 23, at a conference at Fordham University in New York — saying the new directorate would be stood up on Oct. 1 and be led by Anne Neuberger. Neuberger has been leading what NSA used to call the “Russia Small Group,” now renamed the “Election Security Group,” according to an excellent piece on the reshuffle by Shannon Vavra at Cyberscoop. The Election Security Group works in tandem with the FBI, the CIA and the Department of Homeland Security to prevent Russian meddling in election results.
According to the Cyberscoop piece, one of the central missions of the Cybersecurity Directorate will be to share information about newly discovered network vulnerabilities and threat warnings with industry and the general public, such as NSA’s most recent warning for Windows users to patch against the security flaw known as BlueKeep. Bluekeep attacks Microsoft’s Remote Desktop Services software, on Windows XP through to Server 2008, and gives the attacker control of the targeted machine.

Attorney General William Barr
Meanwhile, at the same Fordham conference sponsored by the FBI, Attorney General William Barr surprised the audience with a bombastic call for the development of technology — and the legal authority — to place “backdoors” on encrypted communications and platforms. As reported by The Washington Post today, Barr’s call to arms is highly controversial — raising immediate objections from privacy groups, academics and the Senate’s most outspoken champion of on-line privacy Ron Wyden.
Regular readers of Breaking Defense will note that, just yesterday, I posted a story about a study detailing why such “back doors” are both technologically and legally infeasible.
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.
