NSA’s Rogers Won’t Say China Did OPM Hack
Posted on
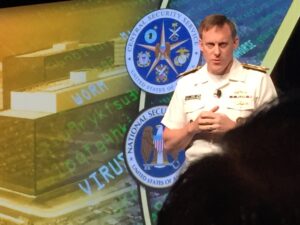
GEOINT: NSA Director Adm. Mike Rogers pointedly declined today to confirm whether China was behind the massive Office of Personnel Management hacks.
“So what really makes you think that, as the head of NSA and Cyber Com, I’m going to talk with you about this,” he told a reporter here today.
Breaking D readers can rely on the expert analysis done for us by John Quigg in his recent op-ed on the subject, but Rogers’ response did seem a trifle dismissive of a reasonable question asked reasonably in an open forum.
A few moments later, Rogers noted that attribution — figuring out who is attacking you, where they are and who they work for or with — is not quite “the challenge it was 10 years ago.” Hopefully, that means we know the Chinese are behind the OPM attack but Rogers just isn’t willing to say so publicly.
Of more lasting interest, Rogers told the packed auditorium at the Washington D.C. conference center that the federal government had to take a new tack in managing cyber security. “Continually responding to individual incidents just isn’t going to work in the long run,” he said.
Rogers’ comments should be heard in light of the sharply critical reports this year about the Department of Homeland Security — responsible for US cyber security — and a host of other federal agencies by the Government Accountability Office, as well as the Inspectors General for DHS, the Defense Department and others.
If the agencies primarily responsible for cyber security aren’t doing what they were supposed to be doing, there clearly need to be federal standards for such work. Given that virtually everyone in the federal government agrees that NSA does the best work in cybersecurity and physical security, perhaps NSA should be tasked with drafting standards for all federal agencies — not just on encryption.
Finally, Rogers raised an interesting issue — that of how important it is to visualize networks. As an admiral, Rogers got used to seeing the battle picture on computer screens. He noted he could see his enemy, his forces, the geography and several layers of data besides. NSA, it seems, doesn’t have that capability: “What I’ve told the team is, ‘can we start looking at how we partner with the private sector about how we visualize our work.'”
Companies start your business development engines.
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.