Common Cyber Standards Will Steamroller Hold-Outs: DoD Officials
Posted on
WASHINGTON: Three top cyber officials told Congress yesterday they now have the authority to crack heads together and impose common cybersecurity standards across the Defense Department.
Dana Deasy, the Pentagon CIO, told the Senate Armed Services subcommittee on cybersecurity that he “absolutely” has the full support of Acting Defense Secretary Patrick Shanahan to use new congressionally-granted authorities to force reforms. So, he said, expect “a lot of noise” from “people who are going to be very uncomfortable.”
Marine Corps Brig. Gen. Dennis Crall, who heads a congressionally charted Cross Functional Team of cyber experts from across the Defense Department, warned it would be a “bad year” for anyone who wants to cling to the old, fragmented way of doing business.
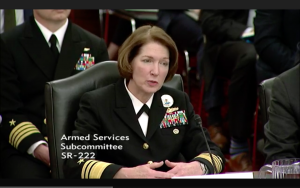
And Navy Vice Adm. Nancy Norton, who heads network defense for Cyber Command, said her HQ is fully operational and has full authority to “issue orders and directives to all DoD components” about securing the department’s 15,000 networks.
Whatcha Gonna Do When They Come For You?
“This is the year now where there will be a lot of noise in the system,” Deasy said, “because we are going to drive those standards, we’re going to drive implementation, and we know there are people who’re going to be very uncomfortable about the fact that we’re no longer going to allow them to stand up their own architectures or solutions.”
“For years… we have allowed services and various components to [develop] and implement unique solutions that maybe aren’t interoperable or stand alone,” Deasy said. “With the new authorities that [my] DoD CIO office was granted starting this year, it now allows my office to establish the standards and the architectures that the components and services have followed.”
(Deasy’s presuming success here: “Have to follow” would probably be more accurate. But it’s testimony to his ferocious confidence).
“You mentioned the fact that we’ve finally published a cyber strategy,” Brig. Gen. Crall told the subcommittee’s skeptical chair and ranking Democrat, Senators Mike Rounds and Joe Manchin. “It’s now time to show results, so I would say this is the year of outcomes.”
“It’s a bad year for those who like endless pilots, pathfinders, and experiments that lead to nowhere,” Crall continued, “a bad year for… those who run off and do business their own way. Lack of standards, individual development and difficulty in integrating, we’re putting an end to that.”
Deasy said he intended to put in place common underlying technologies – software and development tools – that all parts of the Defense Department would need to use, although they could use them in different ways to meet their unique missions. “We need to move beyond the debates of what are the right product sets,” he told the subcommittee. “I’ve always said there’s no reason we need different tools to solve many of these problems. The way we will implement these tools is obviously going to be different if you’re dealing with the tactical edge, an advanced base, versus if you’re going to [be] inside the Pentagon.”
From Acquisition To Operations
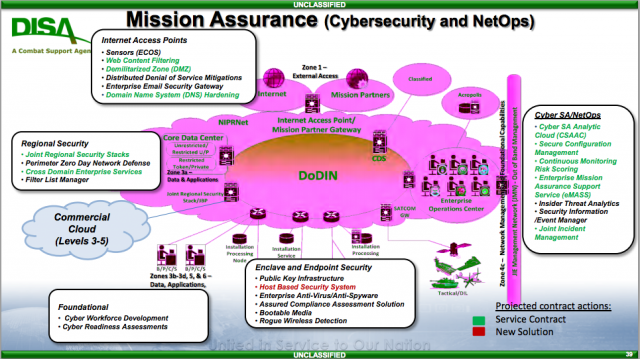
Deasy and Crall are focused on acquisitions: making everyone in the Defense Department develop systems — or, better yet, buy them from the commercial world – that comply to common standards and are compatible with each other. But in the cyber world, you can’t separate acquisitions from operations: Technology changes so quickly, and new threats emerge so suddenly, that you need software developers and frontline operators working side by side. That commercial model, called “DevOps,” has been embraced by Pentagon’s massive (and historically cumbersome) central IT acquisition organization, Defense Information Systems Agency (DISA). What’s more, DISA’s director, Vice Adm. Norton, is also in charge of the operational Joint Force Headquarters protecting the entire Department of Defense Information Network.
JFHQ-DODIN is only four years old, Norton reminded the senators – it didn’t exist when Edward Snowden shoveled reams of secret files over to Wikileaks, she noted – and only reached “Full Operational Capability” in January 2018. But now, she said, she has both the resources and authority to oversee cybersecurity across the Defense Department.
But each piece of DoD is still responsible for its own networks and has its own cybersecurity personnel, noted Sen. Manchin. “They don’t report directly to you,” he said. “Is that a disconnect there?”
“I don’t believe it is,” Norton said. With 43 Defense Department components running 15,000 networks and employing 250,000 cyber personnel, she said, all intimately integrated into the day-to-day operations of everything from Pentagon offices to Air Force squadrons to Navy submarines, it would be impractically cumbersome to put everyone under a single mega-command. But she has six strategic-level Cyber Protection Teams (CPTs) and other cyber experts under her direct control at JFHQ. She also “Directive Authority for Cyberspace Operations [DOCA] over all 43 DoD components,” exercised through a “daily cyber tasking order” and increasingly rigorous inspections. While it’s technically difficult to share cybersecurity data across all the often-incompatible networks, she said, JFHQ-DODIN is “start[ing] to get that visibility for both my forces and US Cyber Command” as a whole.
All these top-down efforts depend on top-level support, which Deasy says he has. When he came aboard as CIO last year, Deasy told the senators, then-Deputy Secretary of Defense Patrick Shanahan told him to create a “CIO working group” that met – and still meets – weekly. “He [Shanahan] was at it every week, he would look for the metrics, he would be quite the tasker, ensuring the activities were getting done,” Deasy said, “and he’s done a very strong handoff to [acting deputy secretary David] Norquist, who’s now continuing that.”
Subscribe to our newsletter
Promotions, new products and sales. Directly to your inbox.